EVM Puzzle 2
Puzzle 2 is very similar to Puzzle 1, with the only difference being that this time we need to understand the CALLVALUE opcode.
👷 I work as a on a daily basis.
 Amazon
AmazonJun 2020 - Current Software Engineer |
 Airbnb
AirbnbApr 2018 - Jul 2020 Full-Stack Engineer |
 Startup Company
Startup CompanyJan 2018 - Feb 2018 Content Creator |
👾 Internship experience:
 ByteDance
ByteDanceOct 2017 - Dec 2017 Software Engineer Intern |
 Google
GoogleJul 2017 - Sep 2017 Software Engineer Intern |
 ByteDance
ByteDanceFeb 2017 - May 2017 Software Engineer Intern |
😄 I'm also passionate about smart contracts and solidity auditing. (Code4rena account: 2997ms, Sherlock account: 2997ms) , feel free to check out and . I have now become a content creator as well, uploading my lectures on smart contracts to Bilibili.
👨💻 Additionally, I love very much.
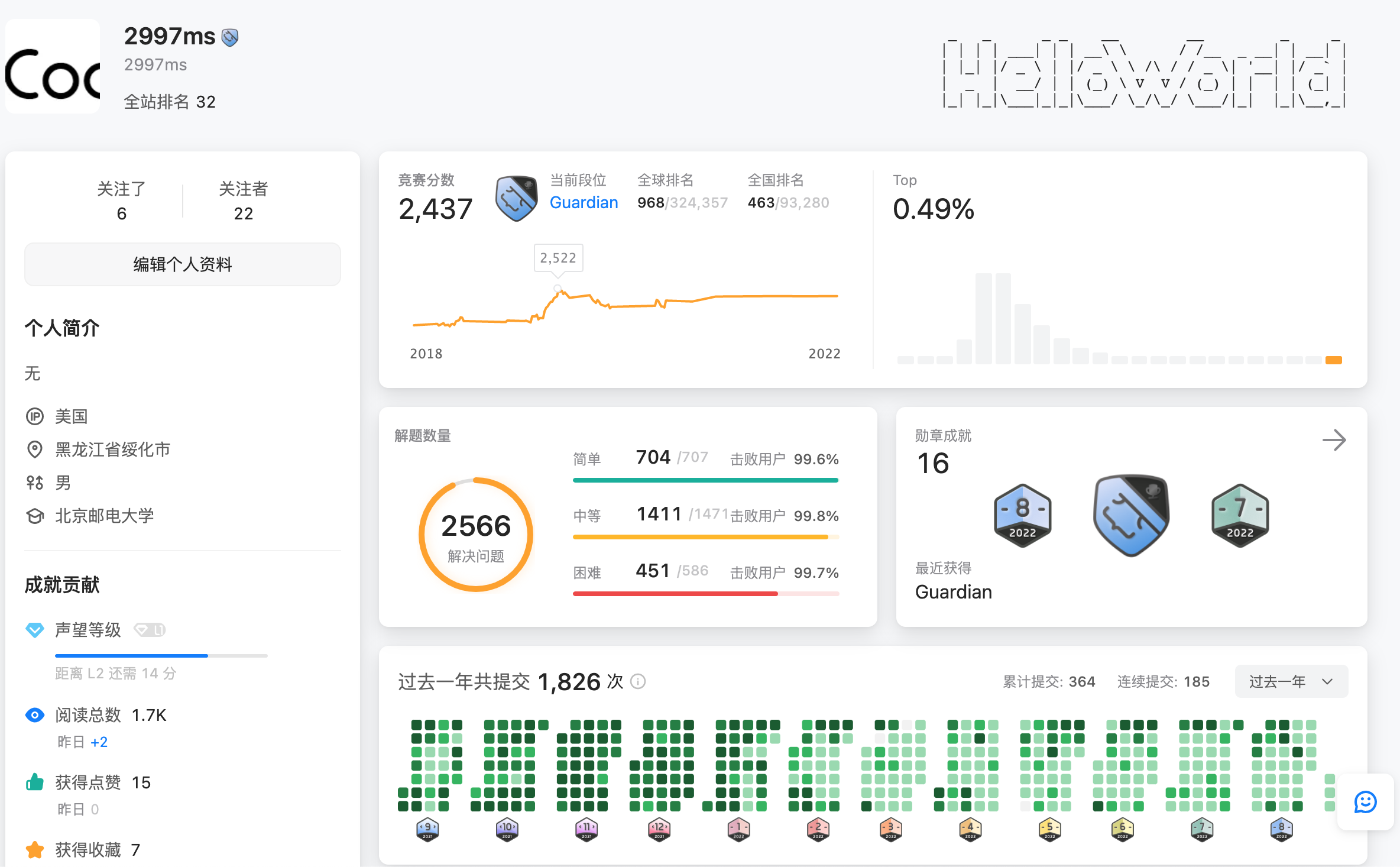
Leetcode Rating 2400+, Solved 3000+ problems
|
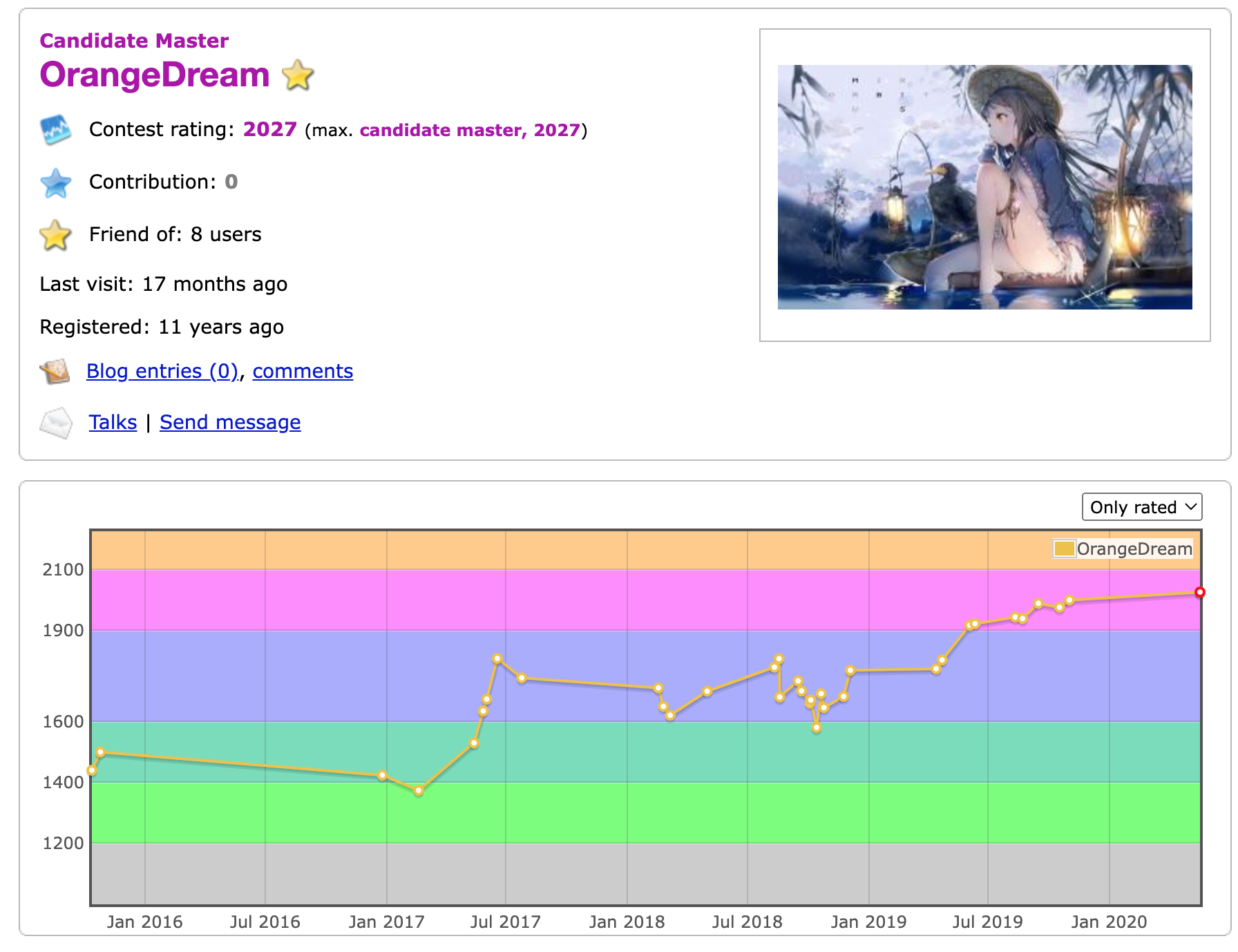
Codeforces Rating 2000+, Solved 967 problems
|
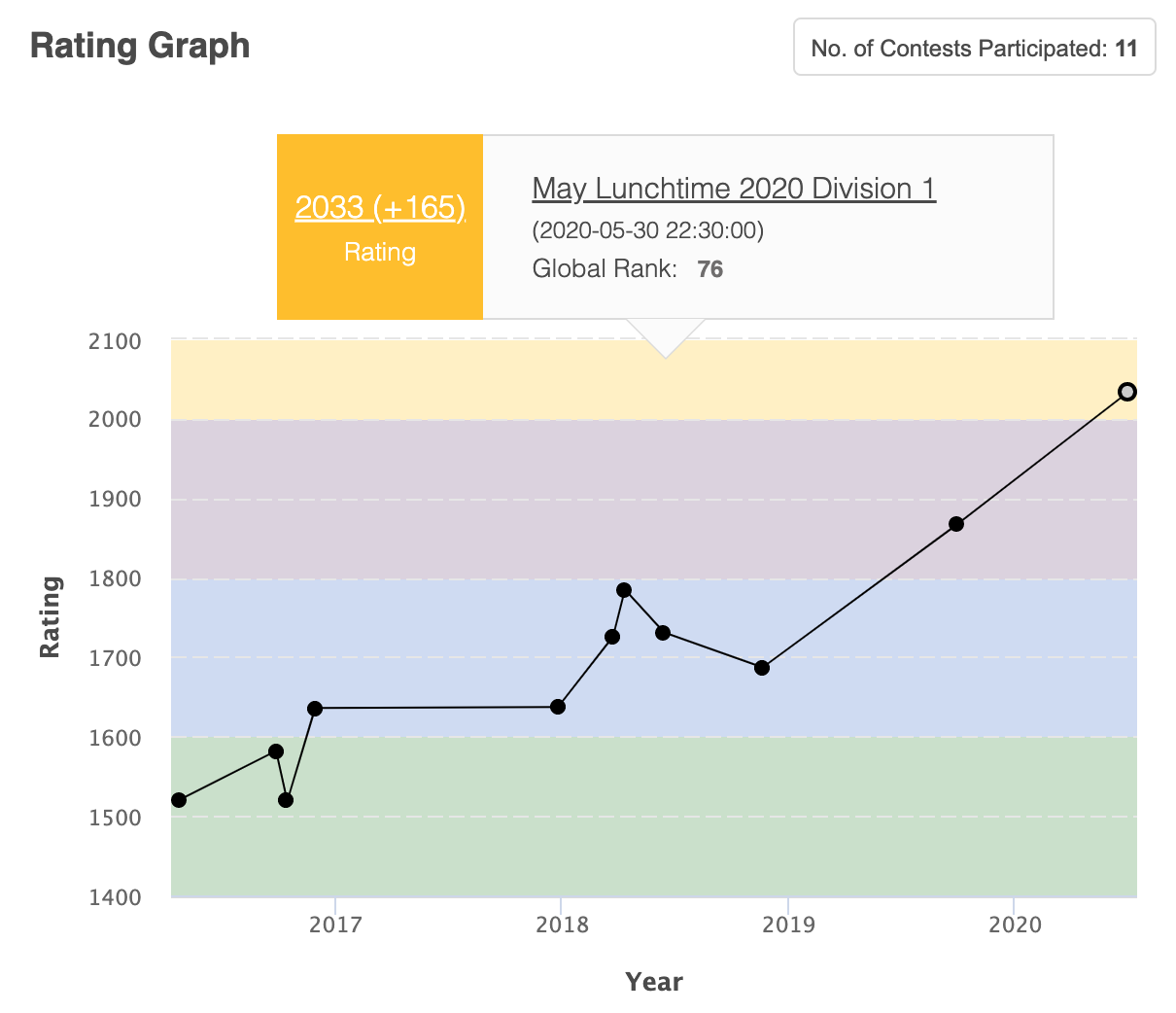
Codechef Rating 2000+
|
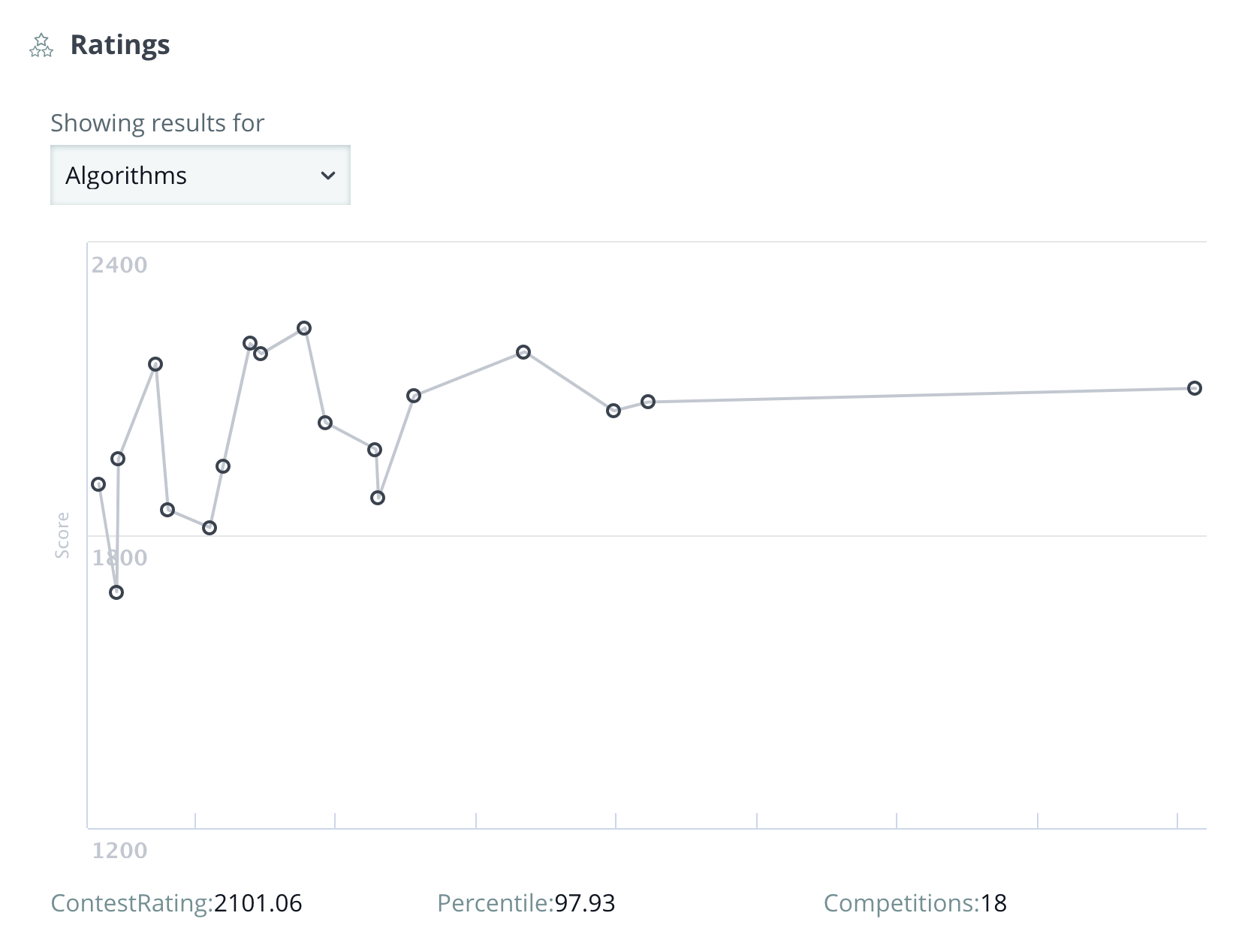
Hackerrank Rating 2100+
|
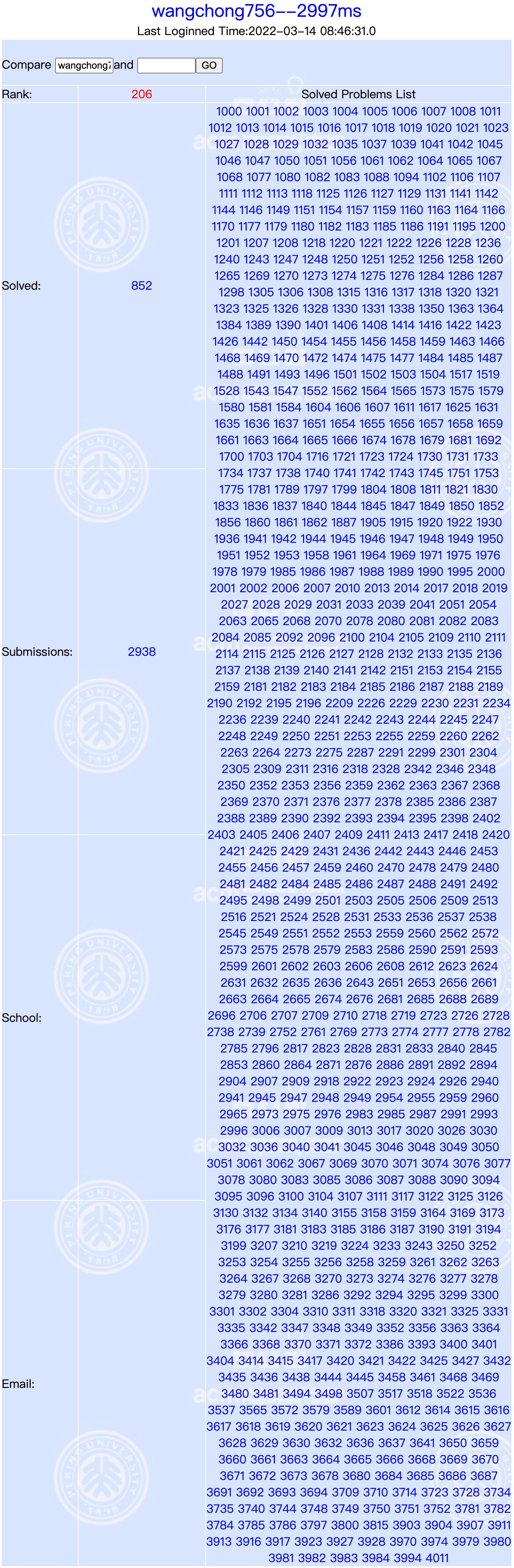
Solved 850+ problems in POJ
|
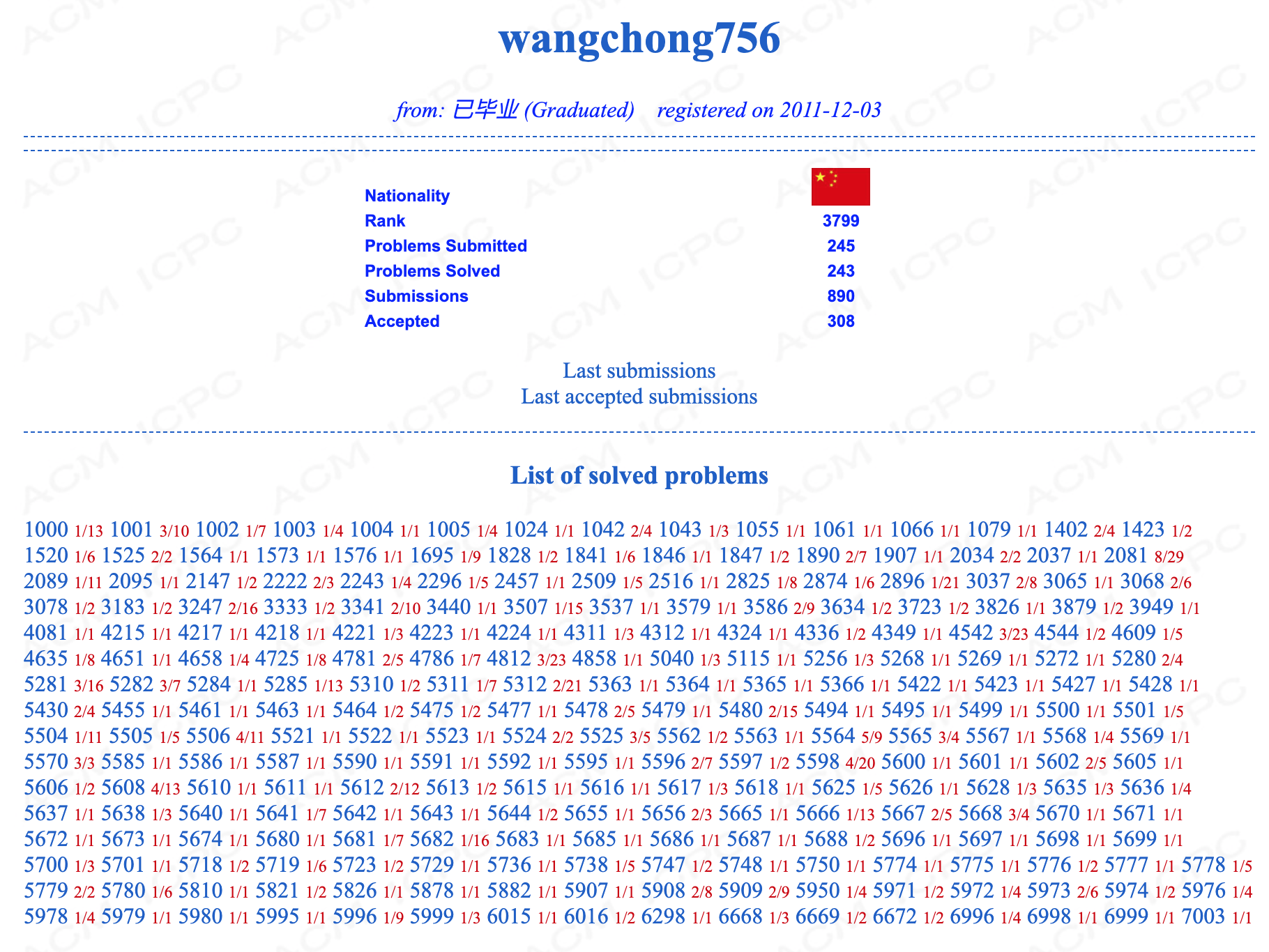
Solved 200+ problems in HDU
 Rank 39 in 51nod
Rank 39 in 51nod
 Level 3, solved 77 problems in ProjectEuler
Level 3, solved 77 problems in ProjectEuler

|
🌎 While I was in , I used to maintain a monthly life summary on CSDN blog (written in Chinese) and my own website (in Chinese). Unfortunately, they are now deprecated.
Puzzle 2 is very similar to Puzzle 1, with the only difference being that this time we need to understand the CALLVALUE opcode.
I recently discovered that the EVM Puzzle series is an excellent set of challenges to test our understanding of EVM opcodes. The puzzles can be found at this link: https://github.com/fvictorio/evm-puzzles. In this blog post, we will focus on solving the first puzzle.
The gist of this question is that the “Recovery” contract created a “SimpleToken” contract but lost the address of the SimpleToken contract. Now, the goal is to find the address of the SimpleToken contract and transfer the ETH inside it.
This question has a difficulty rating of 4 stars and is a very interesting one.
1 | it('Exploit', async function () { |
In ERC20, there is not only transfer function, but also transferfrom function.
In this question, even if the transfer function is overridden and there is a lockTokens modifier to prevent transfers, the transferFrom function in ERC20 is not overridden. We can utilize this function to perform transfers.
This question requires calculating an XOR value. To get the XOR value, we need to perform XOR operation again. The way the XOR value was originally calculated in the problem statement is the same logic that needs to be implemented in our smart contract code to get the XOR value.
This question is actually straightforward. It is similar to the previous one, but this time it requires brute force and understanding the value logic of unit32, uint64, uint160
This task is about how we store the varaibles in Solidity, how solidity allocates space for these variables.
This challenge requires us to change the value of top in the contract to true. By reading the logic of the goTo function, we are expected to implement the Building contract ourselves and ensure that the first call to isLastFloor returns false, and the second call returns true.
It is actually not difficult to implement this.